Abusing Exceptions for Code Execution, Part 1
Por um escritor misterioso
Last updated 11 junho 2024
A common offensive technique used by operators and malware developers alike has been to execute malicious code at runtime to avoid static detection. Often, methods of achieving runtime execution have focused on placing arbitrary code into executable memory that can then be executed. In this article, we will explore a
A common offensive technique used by operators and malware developers alike has been to execute malicious code at runtime to avoid static detection. Often, methods of achieving runtime execution have focused on placing arbitrary code into executable memory that can then be executed. In this article, we will explore a new approach to executing runtime code that does not rely on finding executable regions of memory, but instead relies on abusing existing trusted memory to execute arbitrary code.
A common offensive technique used by operators and malware developers alike has been to execute malicious code at runtime to avoid static detection. Often, methods of achieving runtime execution have focused on placing arbitrary code into executable memory that can then be executed. In this article, we will explore a new approach to executing runtime code that does not rely on finding executable regions of memory, but instead relies on abusing existing trusted memory to execute arbitrary code.

The Top 100 Software Companies of 2023

Project Zero: Injecting Code into Windows Protected Processes using COM - Part 2

101 Landing Page Optimization Tips & Ideas

GitHub Actions Security Best Practices [cheat sheet included]

How Dare They Peep into My Private Life?”: Children's Rights Violations by Governments that Endorsed Online Learning During the Covid-19 Pandemic

InnoGear Boom Arm Microphone Mic Stand for Blue Yeti HyperX QuadCast SoloCast Snowball Fifine Shure SM7B and other Mic, Medium : Musical Instruments

Top 10 secure C++ coding practices - Incredibuild
The UTI Emergency Kit
How to Fix a Toxic Culture

Arbitrary Code Execution - an overview
Recomendado para você
-
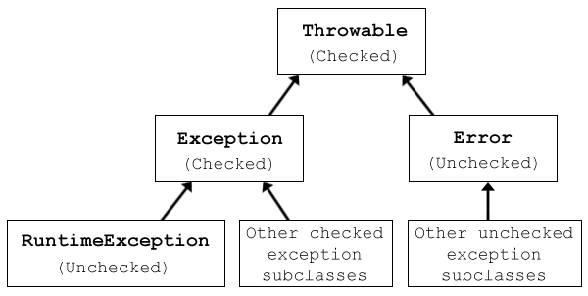 Java Exception Handling: 20 Best Practices for Error-Free Code11 junho 2024
Java Exception Handling: 20 Best Practices for Error-Free Code11 junho 2024 -
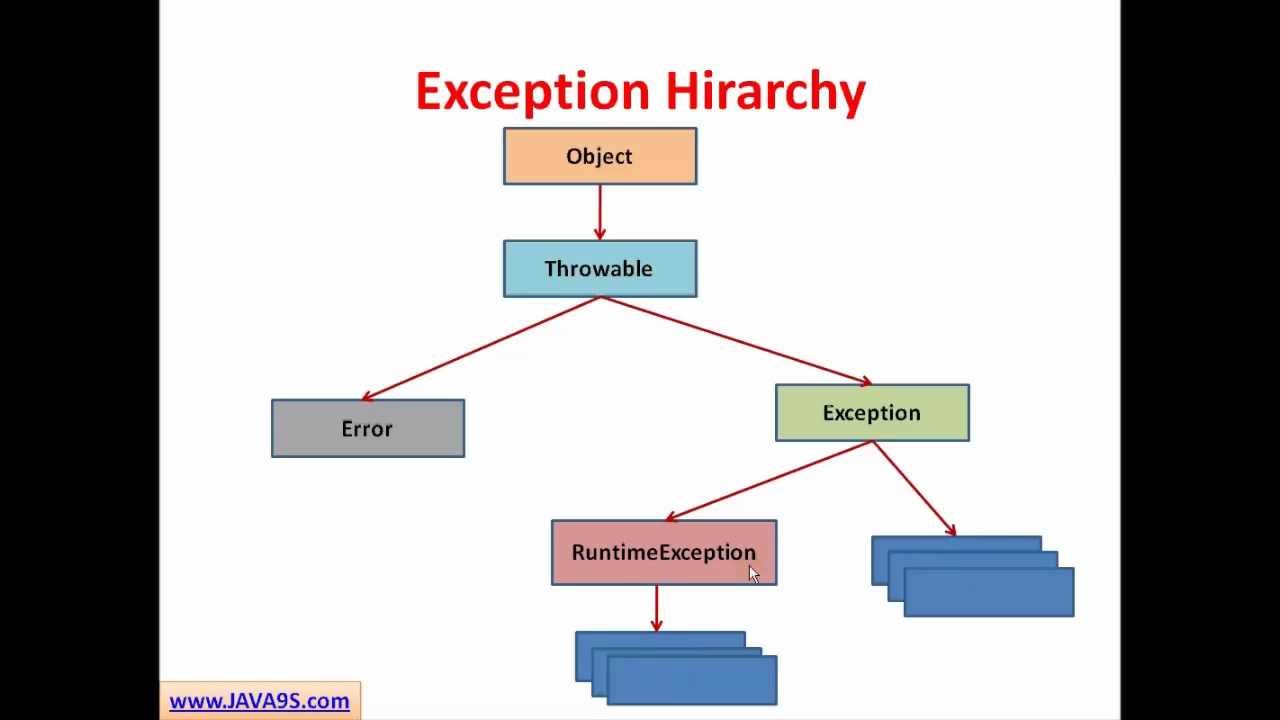 Java Tutorial # 14 Exception Handling in Java - Checked and Unchecked Exceptions11 junho 2024
Java Tutorial # 14 Exception Handling in Java - Checked and Unchecked Exceptions11 junho 2024 -
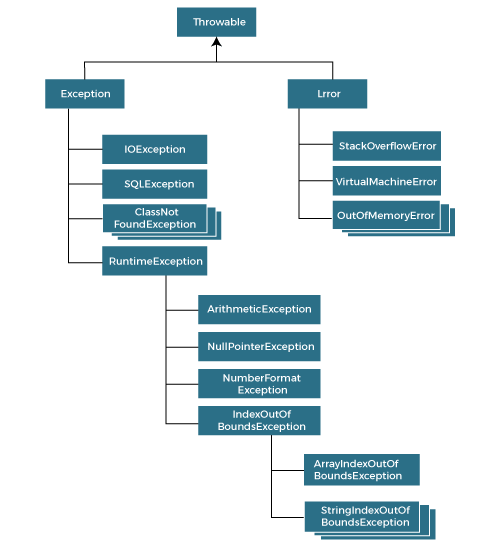 Exception Handling in Java Java Exceptions - javatpoint11 junho 2024
Exception Handling in Java Java Exceptions - javatpoint11 junho 2024 -
 How to Throw Exceptions (The Java™ Tutorials > Essential Java Classes > Exceptions)11 junho 2024
How to Throw Exceptions (The Java™ Tutorials > Essential Java Classes > Exceptions)11 junho 2024 -
 Python's raise: Effectively Raising Exceptions in Your Code – Real Python11 junho 2024
Python's raise: Effectively Raising Exceptions in Your Code – Real Python11 junho 2024 -
 Python Exceptions: The Ultimate Beginner's Guide (with Examples)11 junho 2024
Python Exceptions: The Ultimate Beginner's Guide (with Examples)11 junho 2024 -
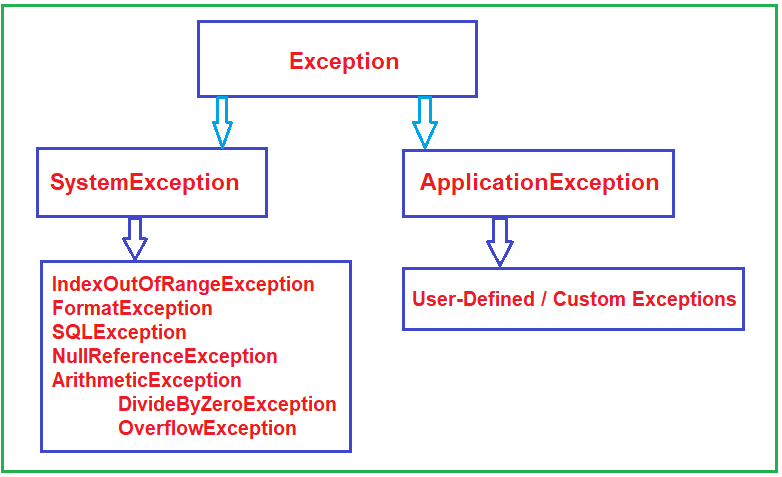 How to Create Custom Exception in C# - Dot Net Tutorials11 junho 2024
How to Create Custom Exception in C# - Dot Net Tutorials11 junho 2024 -
 Auditing Exceptions and How They Might Impact Your SOC Reports11 junho 2024
Auditing Exceptions and How They Might Impact Your SOC Reports11 junho 2024 -
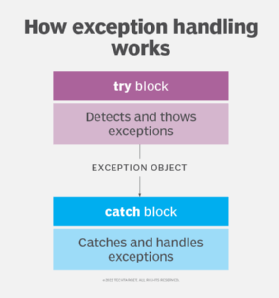 What is Exception Handling? - SearchSoftwareQuality11 junho 2024
What is Exception Handling? - SearchSoftwareQuality11 junho 2024 -
 Exceptions in Snowflake Stored Procedures - ThinkETL11 junho 2024
Exceptions in Snowflake Stored Procedures - ThinkETL11 junho 2024
você pode gostar
-
 Vanitas No Carte GIF - Vanitas No Carte - Discover & Share GIFs11 junho 2024
Vanitas No Carte GIF - Vanitas No Carte - Discover & Share GIFs11 junho 2024 -
 RUDEUS VS GALLUS CLEANER! - React Mushoku Tensei EP 1411 junho 2024
RUDEUS VS GALLUS CLEANER! - React Mushoku Tensei EP 1411 junho 2024 -
 Forest Fall (Cc Free) Download : r/sims211 junho 2024
Forest Fall (Cc Free) Download : r/sims211 junho 2024 -
 ⚡CONTA DE XBOX 360 CHEIA DE JOGOS⚡11 junho 2024
⚡CONTA DE XBOX 360 CHEIA DE JOGOS⚡11 junho 2024 -
 Feelyou Equipamento agrícola de desenho animado caminhões tapeçaria de trator de parede para crianças meninos meninas crianças colheitadeira trator cobertor de parede ultra macio decoração maquinaria caminhão arte de parede médio 5911 junho 2024
Feelyou Equipamento agrícola de desenho animado caminhões tapeçaria de trator de parede para crianças meninos meninas crianças colheitadeira trator cobertor de parede ultra macio decoração maquinaria caminhão arte de parede médio 5911 junho 2024 -
 Jogos reais de estacionamento 3D versão móvel andróide iOS apk11 junho 2024
Jogos reais de estacionamento 3D versão móvel andróide iOS apk11 junho 2024 -
Anime Corner - Ayanokoji can be really scary Vote for Classroom of the Elite S2: acani.me/summer22-v0311 junho 2024
-
Opening the Cheat console on Mac - Answer HQ11 junho 2024
-
 Galaxy S23 FE Review - MORE THAN IT LOOKS11 junho 2024
Galaxy S23 FE Review - MORE THAN IT LOOKS11 junho 2024 -
Samsung A23 5G Prepaid - Tracfone11 junho 2024


