Malware analysis Malicious activity
Por um escritor misterioso
Last updated 31 maio 2024

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Brute Force Attacks: Password Protection

How to build a malware analysis sandbox with Elastic Security

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Malware Analysis: Steps & Examples - CrowdStrike

Free Cybersecurity Training and Career Development

Playbook for Malware outbreak
TryHackMe Hacktivities
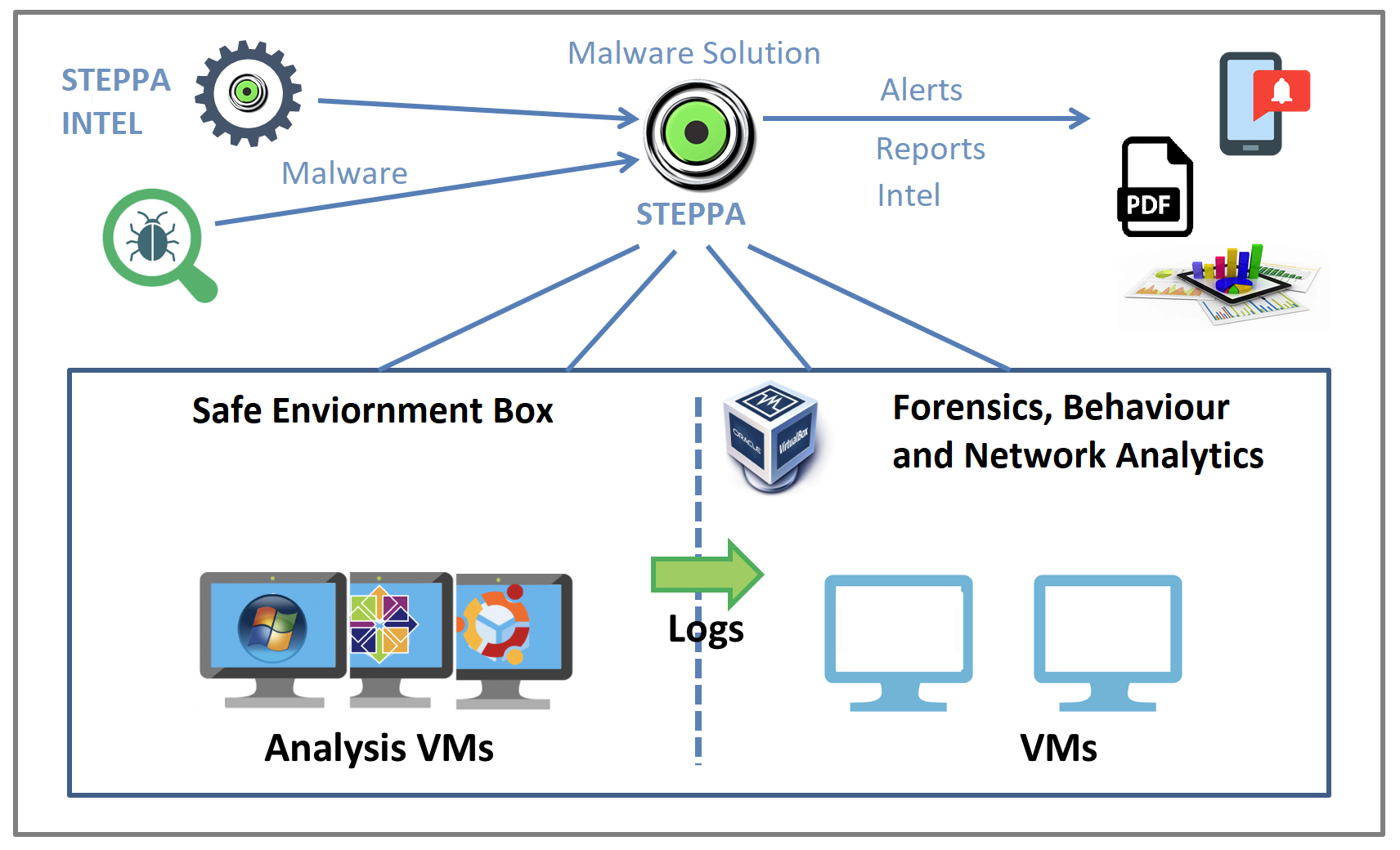
Malware Analysis Solution: Analyze, Detect, and Protect

What is Malware? Definition, Types, Prevention - TechTarget

Malware analysis lockysample.bin.zip Malicious activity

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs
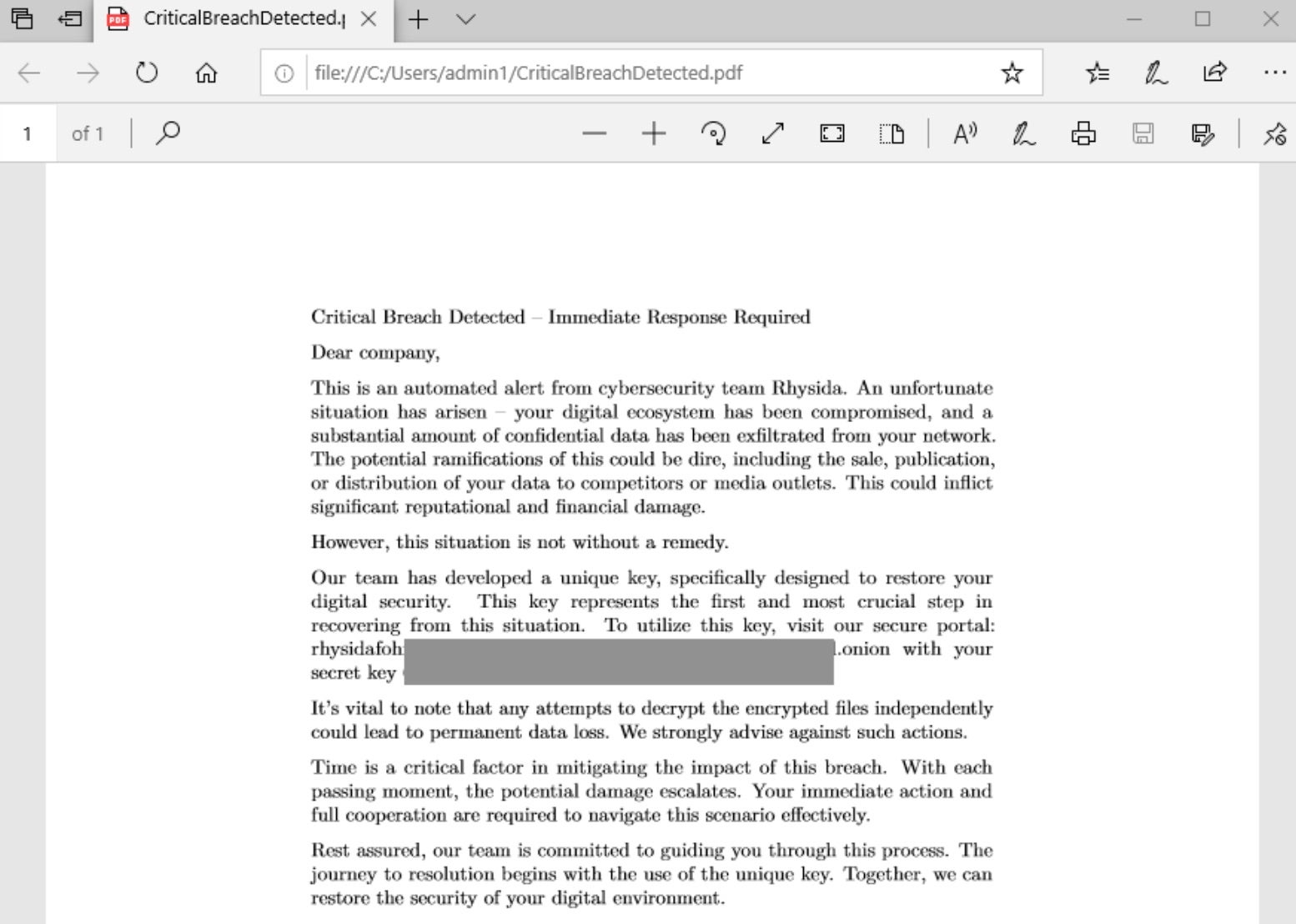
Rhysida - SentinelOne

Malware Analysis Benefits Incident Response
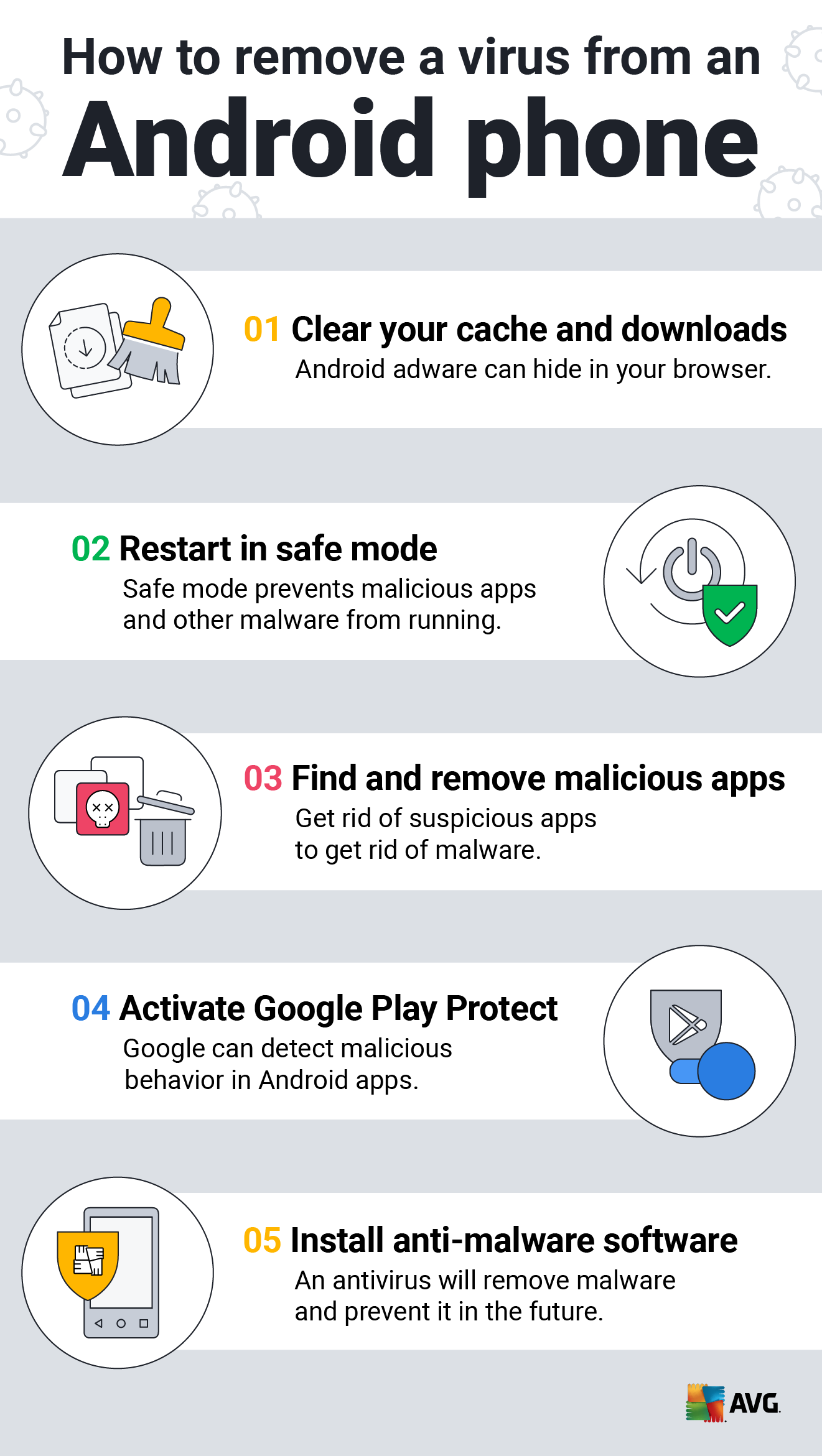
How to Clean an Android or iPhone from Viruses for Free
Recomendado para você
-
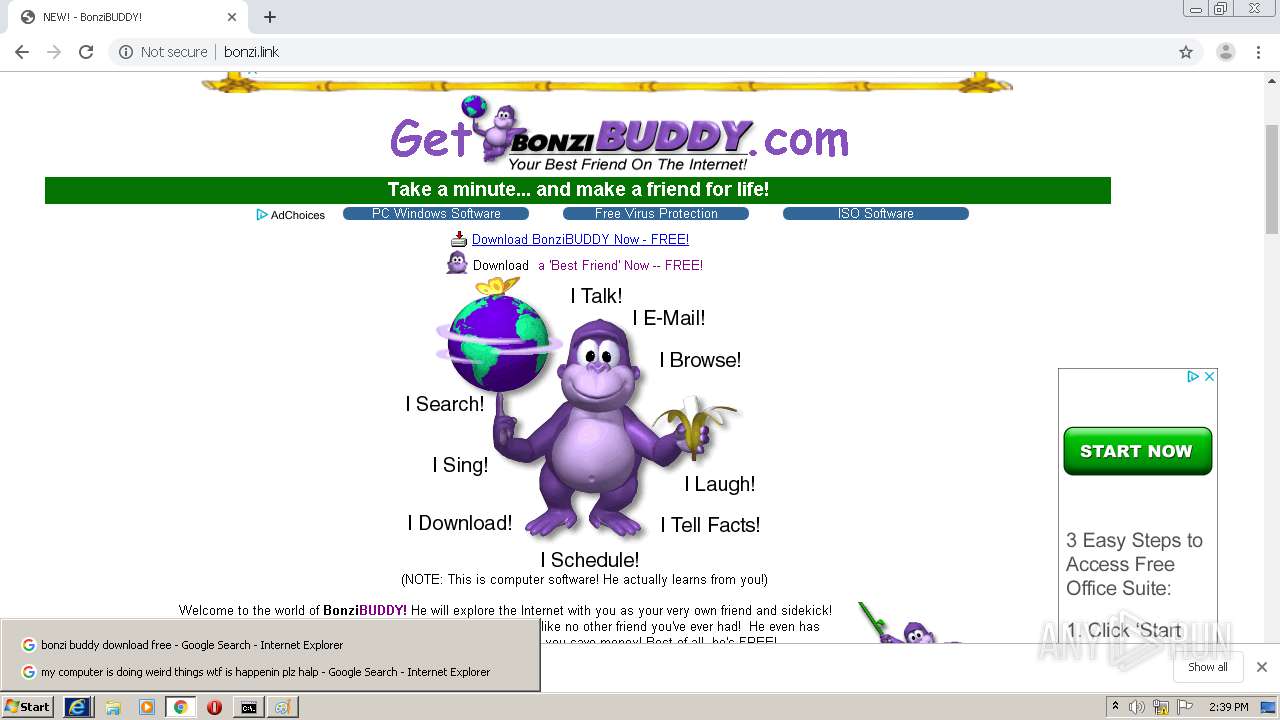
![Fun with Bonzi Buddy Virus (BonziKill) [CRAZY]](https://i.ytimg.com/vi/vLVEsg25Hlk/maxresdefault.jpg) Fun with Bonzi Buddy Virus (BonziKill) [CRAZY]31 maio 2024
Fun with Bonzi Buddy Virus (BonziKill) [CRAZY]31 maio 2024 -
 The Story of BonziBuddy (1999-2004)31 maio 2024
The Story of BonziBuddy (1999-2004)31 maio 2024 -
Steam Workshop::Bonzi Buddy31 maio 2024
-
 bonzi buddy computer class by InfiltratedLines on emaze31 maio 2024
bonzi buddy computer class by InfiltratedLines on emaze31 maio 2024 -
 Chunky Onion on X: Night fam Just downloaded Bonzi Buddy #aesthetic #vaporwave #JK #BonziBuddy / X31 maio 2024
Chunky Onion on X: Night fam Just downloaded Bonzi Buddy #aesthetic #vaporwave #JK #BonziBuddy / X31 maio 2024 -
 Pokemon Bonzi buddy 4831 maio 2024
Pokemon Bonzi buddy 4831 maio 2024 -
![Artwork Design] FREE Animated Bonzi Buddy Windows by joaomolfer on DeviantArt](https://images-wixmp-ed30a86b8c4ca887773594c2.wixmp.com/f/a9c946d7-463f-405c-b788-e3d37859efad/dg0dahn-33d1e61f-8508-4dbb-8506-28054ca93fc7.gif/v1/fill/w_1190,h_671,q_85,strp/_artwork_design__free_animated_bonzi_buddy_windows_by_joaomolfer_dg0dahn-pre.jpg?token=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJzdWIiOiJ1cm46YXBwOjdlMGQxODg5ODIyNjQzNzNhNWYwZDQxNWVhMGQyNmUwIiwiaXNzIjoidXJuOmFwcDo3ZTBkMTg4OTgyMjY0MzczYTVmMGQ0MTVlYTBkMjZlMCIsIm9iaiI6W1t7ImhlaWdodCI6Ijw9ODYyIiwicGF0aCI6IlwvZlwvYTljOTQ2ZDctNDYzZi00MDVjLWI3ODgtZTNkMzc4NTllZmFkXC9kZzBkYWhuLTMzZDFlNjFmLTg1MDgtNGRiYi04NTA2LTI4MDU0Y2E5M2ZjNy5naWYiLCJ3aWR0aCI6Ijw9MTUyOCJ9XV0sImF1ZCI6WyJ1cm46c2VydmljZTppbWFnZS5vcGVyYXRpb25zIl19.s41GswK-78o9G2NpUhZ00GdqxaIWd09wIDeRHQr8TZc) Artwork Design] FREE Animated Bonzi Buddy Windows by joaomolfer on DeviantArt31 maio 2024
Artwork Design] FREE Animated Bonzi Buddy Windows by joaomolfer on DeviantArt31 maio 2024 -
 BonziBUDDY ported to Mac OS X, world leaders breathe sigh of relief31 maio 2024
BonziBUDDY ported to Mac OS X, world leaders breathe sigh of relief31 maio 2024 -
 Bonzi memes. Best Collection of funny Bonzi pictures on iFunny Brazil31 maio 2024
Bonzi memes. Best Collection of funny Bonzi pictures on iFunny Brazil31 maio 2024 -
bonzi buddy 3D Models to Print - yeggi31 maio 2024
você pode gostar
-
 Riot Games' LCS broadcast observes moment of silence for Black Lives Matter - ESPN31 maio 2024
Riot Games' LCS broadcast observes moment of silence for Black Lives Matter - ESPN31 maio 2024 -
 Sizzix Big Shot Foldaway Machine Only (White & Gray)31 maio 2024
Sizzix Big Shot Foldaway Machine Only (White & Gray)31 maio 2024 -
 Convite online carnaval editar grátis31 maio 2024
Convite online carnaval editar grátis31 maio 2024 -
 Boneca Bebê Tipo Reborn - Kit Acessórios na Americanas Empresas31 maio 2024
Boneca Bebê Tipo Reborn - Kit Acessórios na Americanas Empresas31 maio 2024 -
 Super Cat World : Syobon Action Apk Download for Android- Latest31 maio 2024
Super Cat World : Syobon Action Apk Download for Android- Latest31 maio 2024 -
 Jogo de Damas e Xadrez · Legami · El Corte Inglés31 maio 2024
Jogo de Damas e Xadrez · Legami · El Corte Inglés31 maio 2024 -
 Hit-and-heal-yourself-tank, Reacting to SS Dawn and Cresselia31 maio 2024
Hit-and-heal-yourself-tank, Reacting to SS Dawn and Cresselia31 maio 2024 -
 The Forest Review31 maio 2024
The Forest Review31 maio 2024 -
jogo dos pontinhos carlinhos maia|Pesquisa do TikTok31 maio 2024
-
 The Witcher Video Game Reviews and Previews PC, PS4, Xbox One and mobile31 maio 2024
The Witcher Video Game Reviews and Previews PC, PS4, Xbox One and mobile31 maio 2024