Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's Red Team Tools
Por um escritor misterioso
Last updated 11 junho 2024

We analyzed tactics, techniques, and procedures utilized by threat actors of the FireEye’s stolen Red Team Tools. Attackers heavily used various defense evasion techniques.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.

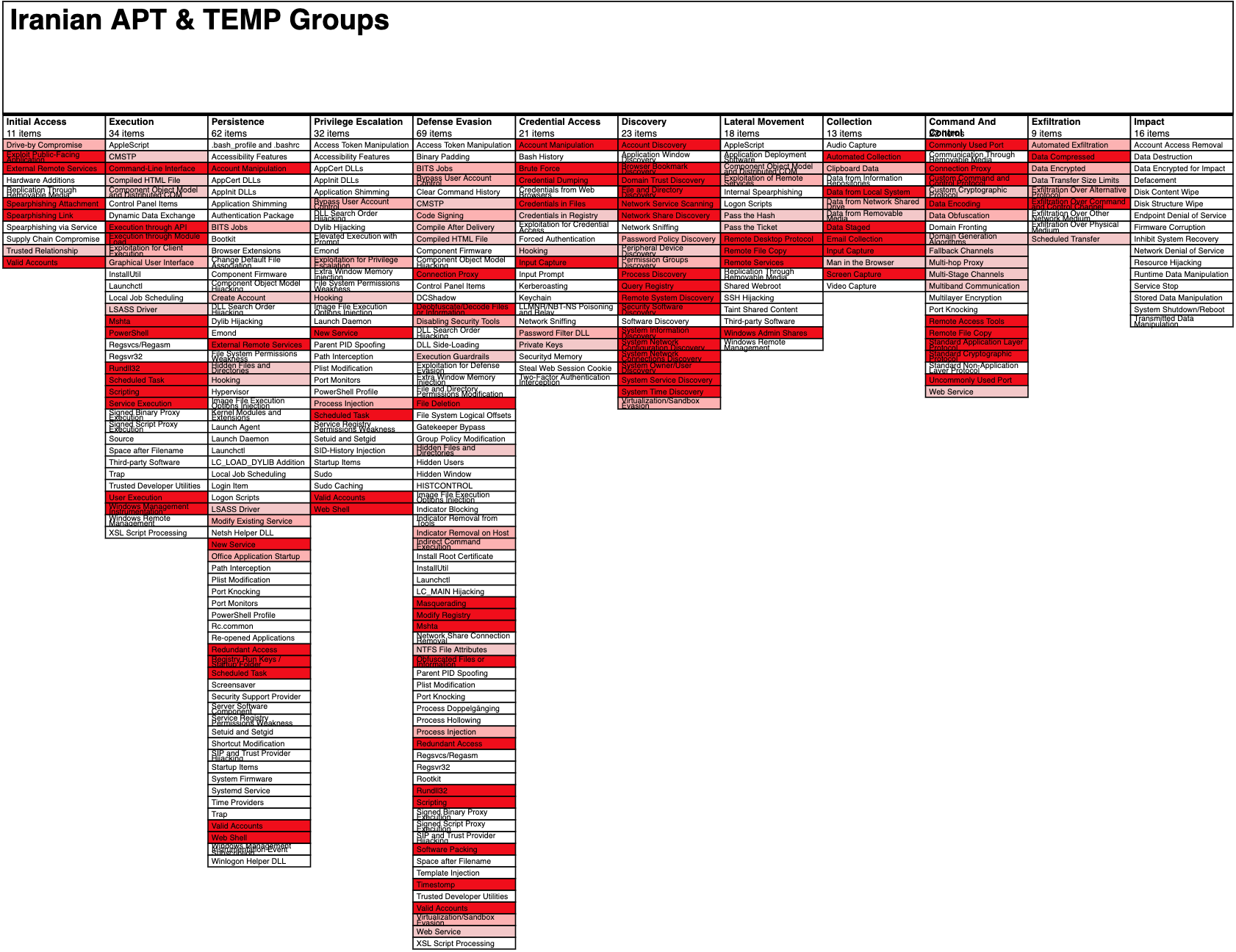
What are Advance Persistent Threats (APT)?
Operationalizing CTI: Using MITRE ATT&CK to Hunt for and Defend
Picus Labs analyzed all the 60 stolen FireEye red team tools and
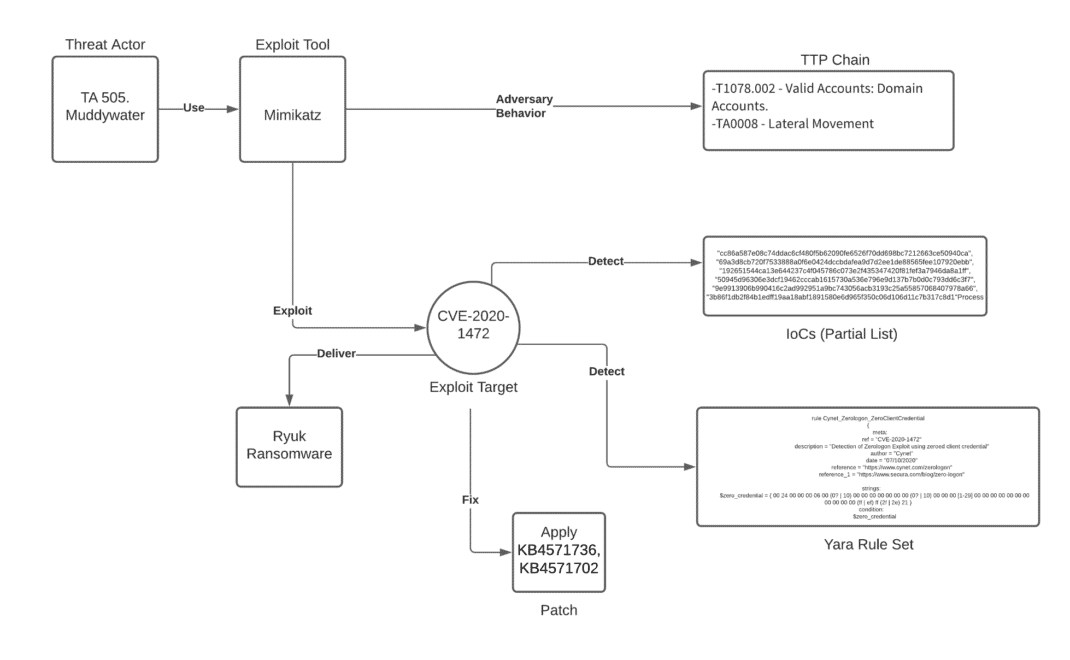
Unpacking the CVEs in the FireEye Breach - Start Here First
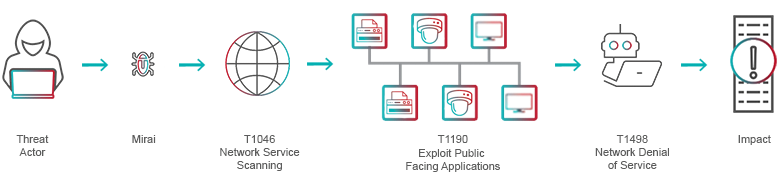
Tactics, Techniques and Procedures

FireEye, one of the world's largest security firms, discloses
Hacking Operational Technology for Defense

FireEye Reveals How SolarWinds Hackers Bypassed the Defenses
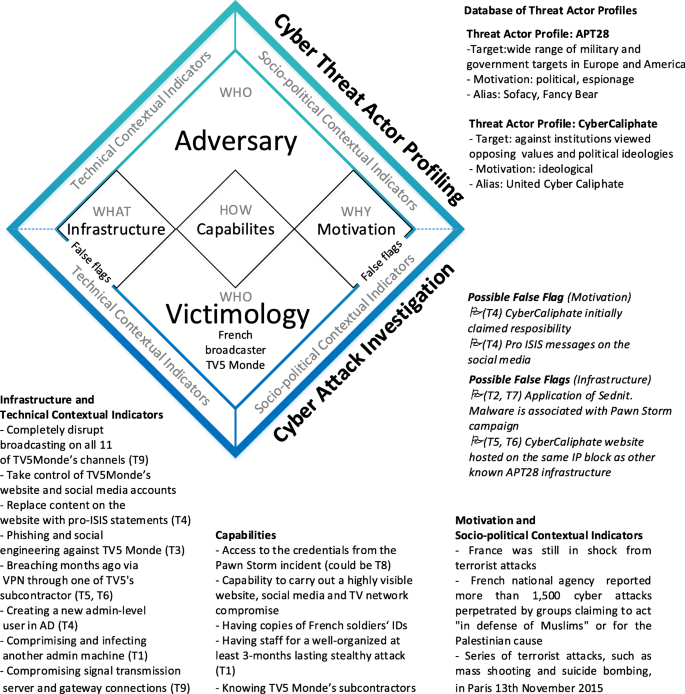
Under false flag: using technical artifacts for cyber attack

FireEye Hack: Sizing Up the Impact - BankInfoSecurity

Techniques Tactics Procedures Utilized by Fireeye Red Team Tools

The Stolen FireEye Red Team Tools Are Mostly Open Source
Recomendado para você
-
 No GPS, No Problem: Honeywell Invents, Demonstrates Military-Grade11 junho 2024
No GPS, No Problem: Honeywell Invents, Demonstrates Military-Grade11 junho 2024 -
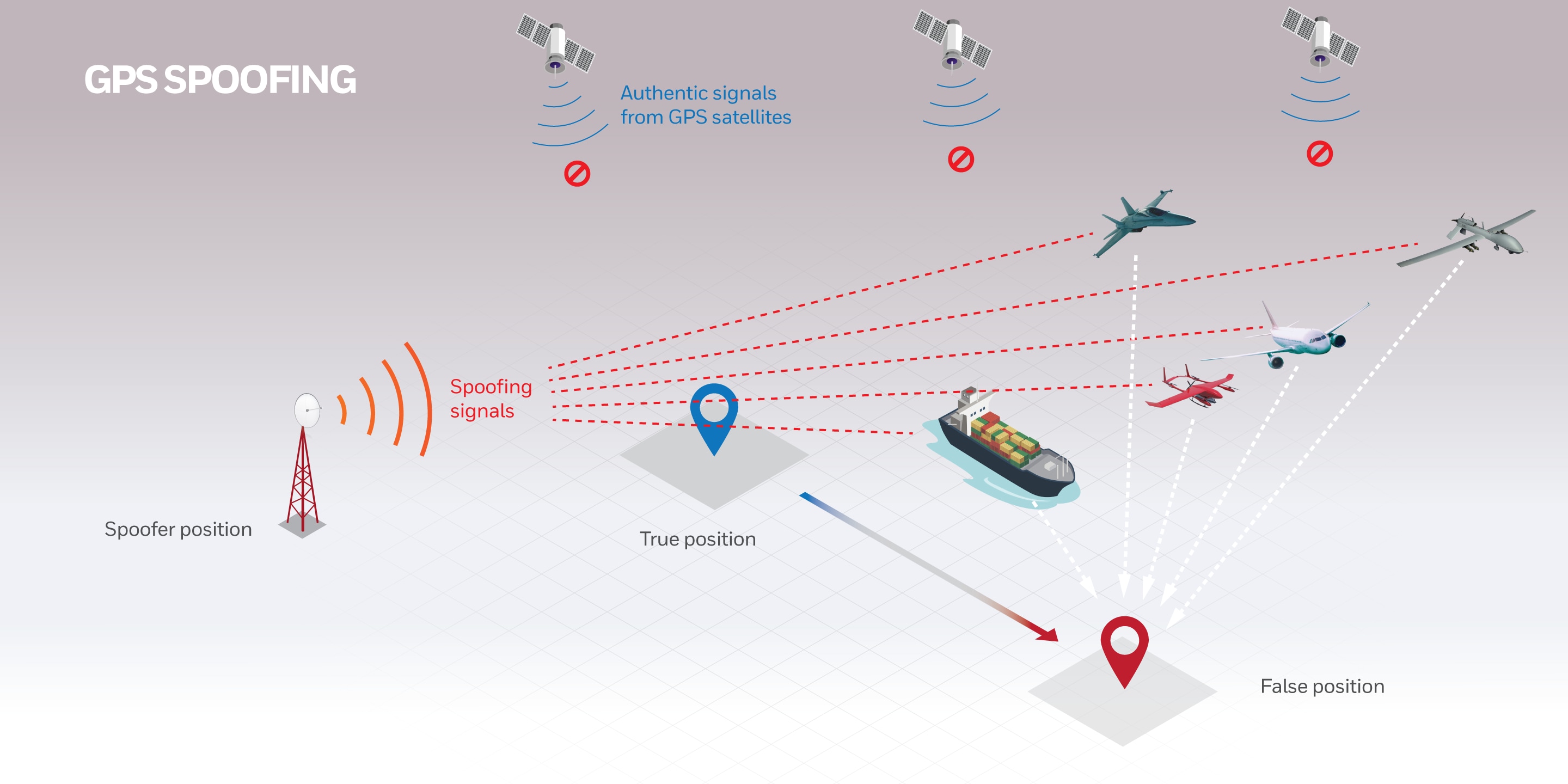
 Spoofers Revealed11 junho 2024
Spoofers Revealed11 junho 2024 -
CHEAPEST RED ENGINE SPOOFER, Video Gaming, Gaming Accessories11 junho 2024
-
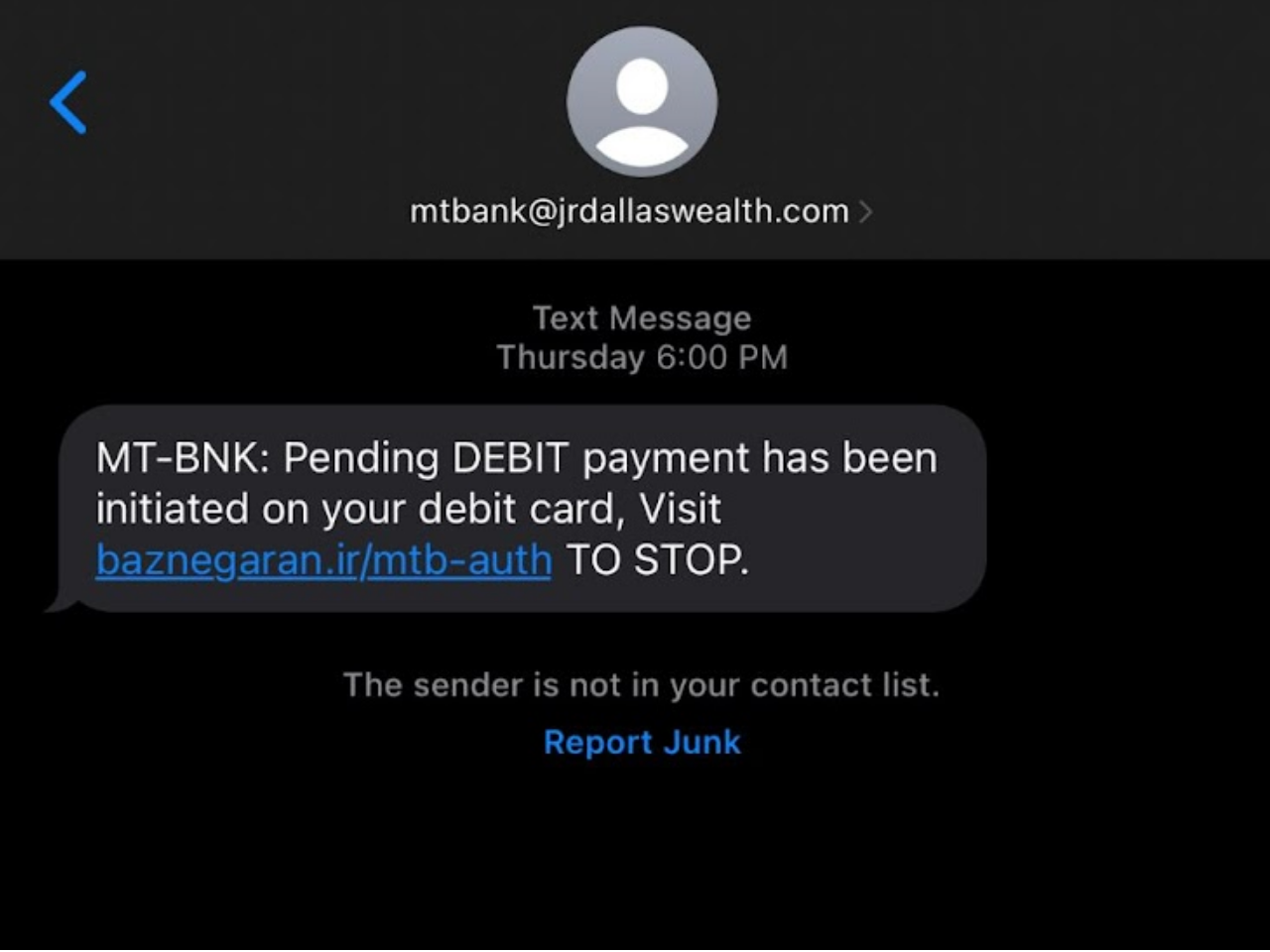 What Is Spoofing In Cybersecurity?11 junho 2024
What Is Spoofing In Cybersecurity?11 junho 2024 -
 Licensing11 junho 2024
Licensing11 junho 2024 -
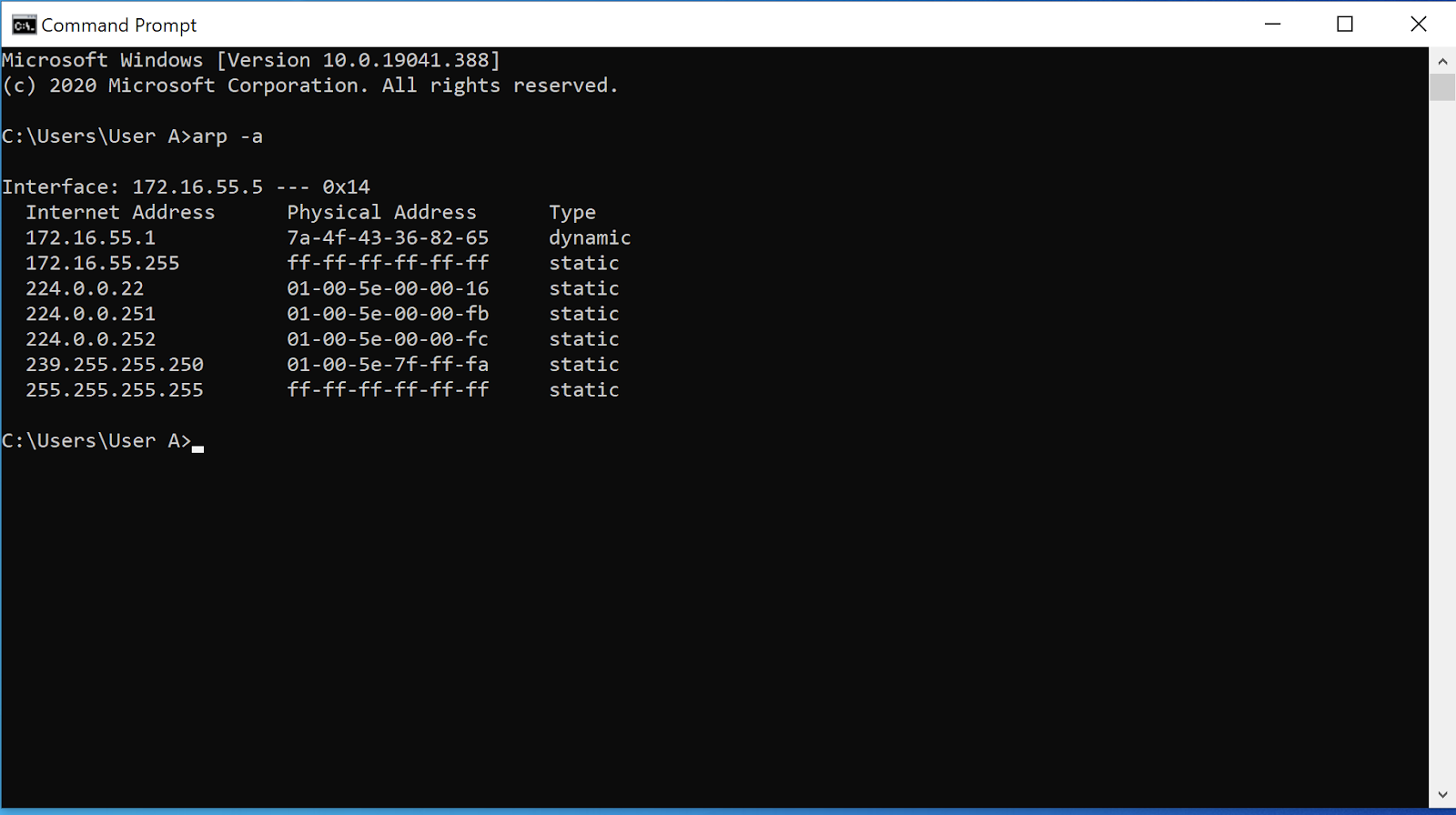 ARP Poisoning: What it is & How to Prevent ARP Spoofing Attacks11 junho 2024
ARP Poisoning: What it is & How to Prevent ARP Spoofing Attacks11 junho 2024 -
 How Do MAC Spoofing Attacks Work?11 junho 2024
How Do MAC Spoofing Attacks Work?11 junho 2024 -
HookSpoofer: The Modified Open Source Stealer Bundlers Making the Rounds11 junho 2024
-
 Protecting GPS From Spoofers Is Critical to the Future of11 junho 2024
Protecting GPS From Spoofers Is Critical to the Future of11 junho 2024 -
 DeepPOSE: Detecting GPS spoofing attack via deep recurrent neural11 junho 2024
DeepPOSE: Detecting GPS spoofing attack via deep recurrent neural11 junho 2024
você pode gostar
-
League of Legends: jogador brasileiro banido por ser tóxico11 junho 2024
-
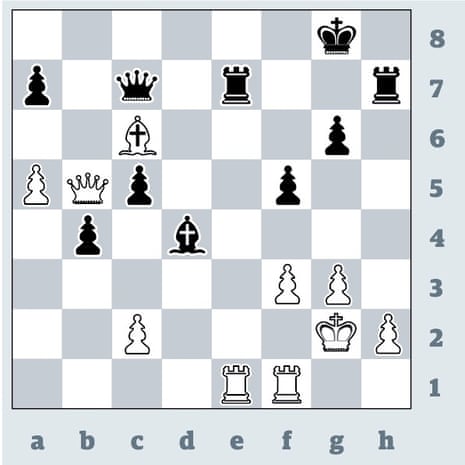 Fabiano Caruana climbs chess rankings after London Classic draw epidemic, Fabiano Caruana11 junho 2024
Fabiano Caruana climbs chess rankings after London Classic draw epidemic, Fabiano Caruana11 junho 2024 -
Will Champion and Freddie Hendrix joined me today for a great days fishing. I appreciate you guys coming to join us here in Steinhatchee.…11 junho 2024
-
 Genshin Impact recebe nova região e novos personagens11 junho 2024
Genshin Impact recebe nova região e novos personagens11 junho 2024 -
 Chris Evans Biography: Age, Gender, Wiki, Net Worth in 202311 junho 2024
Chris Evans Biography: Age, Gender, Wiki, Net Worth in 202311 junho 2024 -
 Game HDMI Retro Consoles de Videogame 10.000 Jogos Retrô 4K 2,4G11 junho 2024
Game HDMI Retro Consoles de Videogame 10.000 Jogos Retrô 4K 2,4G11 junho 2024 -
Letras.mus.br - John Lennon 💬11 junho 2024
-
 Read Online - Chapter 0711 junho 2024
Read Online - Chapter 0711 junho 2024 -
 The Missing Pokemon in Scarlet and Violet's Pokedex Shows Dexit Was For Nothing - GameRevolution11 junho 2024
The Missing Pokemon in Scarlet and Violet's Pokedex Shows Dexit Was For Nothing - GameRevolution11 junho 2024 -
 These Kingdom Hearts Figurines are Royally Cute »11 junho 2024
These Kingdom Hearts Figurines are Royally Cute »11 junho 2024


